- Research Article
- Open access
- Published:
Nonblind and Quasiblind Natural Preserve Transform Watermarking
EURASIP Journal on Advances in Signal Processing volume 2010, Article number: 452548 (2010)
Abstract
This paper describes a new image watermarking technique based on the Natural Preserving Transform (NPT). The proposed watermarking scheme uses NPT to encode a gray scale watermarking logo image or text, into a host image at any location. NPT brings a unique feature which is uniformly distributing the logo across the host image in an imperceptible manner. The contribution of this paper lies is presenting two efficient nonblind and quasiblind watermark extraction techniques. In the quasiblind case, the extraction algorithm requires little information about the original image that is already conveyed by the watermarked image. Moreover, the proposed scheme does not introduce visual quality degradation into the host image while still being able to extract a logo with a relatively large amount of data. The performance and robustness of the proposed technique are tested by applying common image-processing operations such as cropping, noise degradation, and compression. A quantitative measure is proposed to objectify performance; under this measure, the proposed technique outperforms most of the recent techniques in most cases. We also implemented the proposed technique on a hardware platform, digital signal processor (DSK 6713). Results are illustrated to show the effectiveness of the proposed technique, in different noisy environments.
1. Introduction
With the widespread use of the Internet and the rapid and massive development of multimedia, there is an impending need for efficient and powerfully effective copyright protection techniques. A variety of image watermarking methods have been proposed [1–14], where most of them are based on the spatial domain [1, 2] or the transform domain [3, 4]. However, in recent years [14–16], several image watermarking techniques based on the transform domain have appeared.
Digital watermarking schemes are typically classified into three categories. Private watermarking which requires the prior knowledge of the original information and secret keys at the receiver. Semiprivate or semiblind watermarking where the watermark information and secret keys must be available at the receiver. Public or blind watermarking where the receiver must only know the secret keys [14]. The robustness of private watermarking schemes is high to endure signal processing attacks. However, they are not feasible in real applications, such as DVD copy protection where the original information may not be available for watermark detection. On the other hand, semi-blind and blind watermarking schemes are more feasible in that situation [12]. However, they have lower robustness than the private watermarking schemes [13]. In general, the requirements of a watermarking system fall into three categories: robustness, visibility, and capacity. Robustness refers to the fact that the watermark must survive against attacks from potential pirates. Visibility refers to the requirement that the watermark be imperceptible to the eye. Capacity refers to the amount of information that the watermark must carry. Embedding a watermark logo typically amounts to a tradeoff occurring between robustness visibility and capacity.
In [15], a composite approach for blind grayscale logo watermarking is presented. This approach is based on the multiresolution fusion principles to embed the grayscale logo in perceptually significant blocks in wavelet subband decompositions of the host image. Moreover, a modulus approach is used to embed a binary counterpart of the logo in the approximation sub-band. However, in spite of its high complexity, the technique failed with the cropping attacks. In [16], a curvelet-based watermarking technique has been proposed for embedding gray-scale logos; however, the normalized correlation (NCORR) between the original and extracted logos with most of the watermarking attacks does not exceed 0.91. Several wavele-based fragile watermarking techniques have been presented in [17–19]. Other similar techniques are also presented but in the DCT domain [20–22]. In spite of the successful performance of most watermarking techniques reported in the literature, they still suffer from being semifragile due to the energy concentration of their transform domains (DCT and Wavelets), which makes them discard much of the mid- and high-frequency watermarked data in compression.
In [5, 7–16, 23, 24], an alternate novel watermarking scheme has been proposed. It is based on making use of the Natural Preserve Transform, NPT. The NPT is a special orthogonal transform class that has been used to code and reconstruct missing signal portions [23]. Unlike previous watermarking schemes that use binary logos, NPT amounts to evenly distributing the watermarking gray-scale logo or text, all over the host image. The method assumes the prior knowledge of the host image for watermark extraction, and it also suffers from slow convergence in the logo extraction process. In [25, 26], an efficient fast least squares technique is proposed for NPT watermark extraction, to remedy the iterative technique originally proposed in [23, 24].
In this paper, a unified approach is proposed for nonblind and quasiblind NPT-based watermarking. In the quasiblind case, the extraction technique requires little information about the original host image that is needed for the complete recovery of both the host image and watermarking logo. This needed information is conveyed by the watermarked image itself with no or negligible degradation. Illustrative examples are given to show the quality of the watermarked images, as well as the extracted watermarking logo and its performance in the presence of attacks. Hardware implementations using DSP have experimentally proved computer simulations. In fact, apart from its simplicity, the method is virtually insensitive to cropping attacks and performs well in case of compression and noise attacks. The proposed approach also delivers an extracted watermark that is not only perfect/semiperfect but also can be visually seen by the user, which gives the application more user confidence and trust.
The paper is organized as follows. Section 2 covers all mathematical background needed for our proposed watermarking technique using NPT. Section 3 briefly reviews the NPT nonblind and blind embedding and extraction techniques and describes their implementation. Experimental procedure and simulation results are presented in Section 4, along with hardware implementation results. Discussion and conclusion are in Sections 5 and 6, respectively.
2. Mathematical Background for NPT
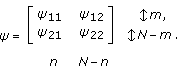
The NPT was first used as a new orthogonal transform that holds some unusual properties that can be used for encoding and reconstructing lost data from images. The NPT transform of an image S of size is given by
is given by

where  is the transformation kernel defined as [23, 24]
is the transformation kernel defined as [23, 24]

where I
N
is the N th order identity matrix,  , and
, and  is any orthogonal transform, like Hadamard, DCT, Hartley, or any other orthogonal transform. Throughout this paper, we use the 2D Hartley transform, defined by
is any orthogonal transform, like Hadamard, DCT, Hartley, or any other orthogonal transform. Throughout this paper, we use the 2D Hartley transform, defined by

We note here that the Hartley transform was utilized due to its circular symmetry performance, as it evenly distributes the energy of the original image in the 4 corners of the orthogonally projected transform image. Hence the Hartley transform achieves a tradeoff point between the energy concentration feature (which is crucial for any transform domain for compression purposes) and the even distribution and spreading feature (which is crucial for watermarking and data hiding applications). Figure 1 illustrates this idea by showing the energy concentration for different well-known orthogonal transforms such as DCT, Wavelet, Hadamard and Hartley.
The value of  in (2), gives a balance between the original domain and the transform domain sample basis. Clearly, when
in (2), gives a balance between the original domain and the transform domain sample basis. Clearly, when  , the transformed image is the original image whereas when
, the transformed image is the original image whereas when  , it will be its orthogonal projection (which is in the Hartley transform as in this paper). Hence the NPT transform is capable of concentrating energy of the image while still preserving its original samples values on a tradeoff basis. This makes the NPT transform domain image has both almost original pixel values (that cannot be visually distinguished from the original image) and mostly capable of retrieving the original image from a small part of the transformed image (provided that this small part has enough energy concentration in it). The transformed image has PSNR of the order
, it will be its orthogonal projection (which is in the Hartley transform as in this paper). Hence the NPT transform is capable of concentrating energy of the image while still preserving its original samples values on a tradeoff basis. This makes the NPT transform domain image has both almost original pixel values (that cannot be visually distinguished from the original image) and mostly capable of retrieving the original image from a small part of the transformed image (provided that this small part has enough energy concentration in it). The transformed image has PSNR of the order  .
.
The original image can be retrieved from the transformed image S tr , using

If H is symmetric, as in Hartley matrices, one can show that  . Otherwise, the matrix
. Otherwise, the matrix  can be computed as follows:
can be computed as follows:  This means that it can be evaluated to any desired accuracy as
This means that it can be evaluated to any desired accuracy as  .
.
Instead of spreading the orthogonal projection over the complete image frame, one can only spread it over part of the image (specific blocks or quarters). This leads to the M th partial NPT that is defined as follows:

Figure 2 shows Lena image and its NPT transformed image.  is adjusted to yield a nominal PSNR of 45 dB. Its value is
is adjusted to yield a nominal PSNR of 45 dB. Its value is  . The PSNR of the transformed image is 44.17 dB. The high similarity between the original and transformed images suggests that NPT is very convenient for watermarking and data hiding.
. The PSNR of the transformed image is 44.17 dB. The high similarity between the original and transformed images suggests that NPT is very convenient for watermarking and data hiding.
3. The Proposed Image Watermarking Technique (IW-NPT)
3.1. Watermark Embedding
Let the host image S (size  ) be watermarked by a watermarking logo w of size (
) be watermarked by a watermarking logo w of size (
 ). In the bottom embedding technique [25], the logo is embedded to S as the last r bottom lines. Hence, the logo matrix is reshaped to be a matrix w
1
(of size
). In the bottom embedding technique [25], the logo is embedded to S as the last r bottom lines. Hence, the logo matrix is reshaped to be a matrix w
1
(of size 
 ). Then, the last r rows of S are replaced by the reshaped logo w
1
. Such step yields a watermarked square image S
wm
,
). Then, the last r rows of S are replaced by the reshaped logo w
1
. Such step yields a watermarked square image S
wm
,  .
.
Next, the NPT of 
 obtained as follows:
obtained as follows:

This step in (6) would register the watermark (distribute its energy) all over the host image. In order to make the watermarking logo invisible, we replace the last r rows z of  with the last r of the original image S. Hence,
with the last r of the original image S. Hence,

In [26], a more simple embedding technique is proposed. It amounts to replacing part of the host image by the logo image. For simplicity, the logo is embedded in the upper left corner. So, if the host image is partitioned as  , then the embedded image is
, then the embedded image is  . Now, the NPT-based watermarking technique proceeds as follows.
. Now, the NPT-based watermarking technique proceeds as follows.
-
(1)
Obtain the NPT of
 as
as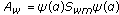 .
. -
(2)
Partition
 (8)
(8) -
(3)
In order to make the watermarking logo invisible, the watermarked image A wm is constructed by replacing the upper left cropped section by the true host image S 11 , that is,
 .
.
It is also worth mentioning that, the logo can be embedded any where in the image [26]. Here, we choose to embed the logo in the image region S
k
that is most similar to the logo, that is, that has the least Euclidian distance .
.
As an illustrative example, we consider the embedding of Assiut University logo, shown in Figure 3 onto Lena image, using the three embedding techniques. The gray-scale Assiut University logo has a size of  . The complete Harley orthogonal transformation is used with
. The complete Harley orthogonal transformation is used with . In the bottom embedding case, the logo is embedded as 21 bottom rows, as described earlier. Figure 4 shows the NPT watermarked image A
w
and the masked watermarked image A
wm
for the bottom, top, and optimum embedding cases. The watermarked PSNRs are 39.85, 39.6, and 39.71 dB., respectively. We note here that top embedding (or embedding in any of the 4 corners) would give the best watermarking and extraction performance as will be shown later. This is due to the more energy concentration in the corner for the Hartley transform (Figure 1).
. In the bottom embedding case, the logo is embedded as 21 bottom rows, as described earlier. Figure 4 shows the NPT watermarked image A
w
and the masked watermarked image A
wm
for the bottom, top, and optimum embedding cases. The watermarked PSNRs are 39.85, 39.6, and 39.71 dB., respectively. We note here that top embedding (or embedding in any of the 4 corners) would give the best watermarking and extraction performance as will be shown later. This is due to the more energy concentration in the corner for the Hartley transform (Figure 1).
3.2. Watermark Extraction
The watermarking extraction process is divided into a nonblind case, where the original host image is known at the receiver side and we only try to extract the logo from the watermarked image, and a blind case where the host image is not known at the receiver side, and we try to extract both the host and logo images from the watermark image, A wm .
3.2.1. The Nonblind Case
We first try to extract the logo from the top embedding watermarked image, as in Figure 4(b). Assuming that the original image S, the parameter  of (1), and the type of the orthogonal transformation H
N
, are known at the receiver, the extraction of the watermark from the received, A
wm
proceeds as follows.
of (1), and the type of the orthogonal transformation H
N
, are known at the receiver, the extraction of the watermark from the received, A
wm
proceeds as follows.
-
(1)
Determine the logo size m, n. This is easily done by correlating the watermarked image A wm to the host image S to determine the region of exact matching, (S11).
-
(2)
Form
 (9)
(9)Due to the insertion of S 11 in place of A 11 ,
 submatrices
submatrices 

 are in error (nonwatermarked) while Y
21
and Y
22
are in error (nonwatermarked) while Y
21
and Y
22
 convey the watermark effects.
convey the watermark effects. -
(3)
Partition
 (10)
(10)
Then, as long as  , the watermark w is the least squares solution of the system
, the watermark w is the least squares solution of the system

Even though Y
22
 not corrupted, we do not need it to calculate the logo w in this nonblind case.
not corrupted, we do not need it to calculate the logo w in this nonblind case.
The quality of extraction is judged by computing the normalized correlation NCORR between the original and extracted logo, that is,

where  is the extracted watermark. The nonblind extracted logo, as in this image, in our experiments achieved a NCORR
is the extracted watermark. The nonblind extracted logo, as in this image, in our experiments achieved a NCORR  1 performance factor. A similar approach is applied in case of bottom embedding or optimum embedding. The technique is straightforward for the 3 cases and computationally efficient while being accurate and fast convergent. For the number of unknowns in (11) to be less or equal to the number of known equations, the watermarking logo must be limited in size, meaning it must not have a number of rows larger than
1 performance factor. A similar approach is applied in case of bottom embedding or optimum embedding. The technique is straightforward for the 3 cases and computationally efficient while being accurate and fast convergent. For the number of unknowns in (11) to be less or equal to the number of known equations, the watermarking logo must be limited in size, meaning it must not have a number of rows larger than  for top, bottom, and optimum embedding cases.
for top, bottom, and optimum embedding cases.
3.2.2. The Quasiblind Case
When the prior knowledge of the host image S is not available, the following quasiblind technique is proposed for watermarking extraction of an NPT-based watermarked image. For simplicity, we consider the blind extraction of bottom embedding logos. The proposed technique can be described as follows.
-
(1)
Partition
 (13)
(13)As
 and from (6), (7), and (9), we can easily show that
and from (6), (7), and (9), we can easily show that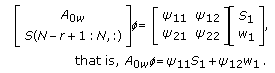 (14)
(14) -
(2)
To cancel the effect of S 1 in (14), construct an
 square matrix V such that
square matrix V such that  . This matrix can be easily constructed by expressing its k th vector V
k
as follows:
. This matrix can be easily constructed by expressing its k th vector V
k
as follows: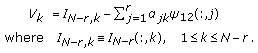 (15)
(15)The
 are obtained by solving a set of r linear equations satisfying the following condition:
are obtained by solving a set of r linear equations satisfying the following condition: (16)
(16)Since
 is an
is an  byr matrix, then its rank
byr matrix, then its rank  . Consequently, the rank of the matrixV is (N
. Consequently, the rank of the matrixV is (N 2r)[27].
2r)[27]. -
(3)
Premultiply (14) by
 to yield
to yield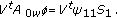 (17)
(17)As the rank of
 is (
is ( ), the rank of
), the rank of  is (
is ( ). So, to have a unique solution of (17), r arbitrary parameters of every column of S
1
have to be known at the receiver/extractor. This can be achieved if in the watermarked image A
w
, we choose the matrix z (6) to beS(N
). So, to have a unique solution of (17), r arbitrary parameters of every column of S
1
have to be known at the receiver/extractor. This can be achieved if in the watermarked image A
w
, we choose the matrix z (6) to beS(N 2r
2r 1 : N
1 : N r,:)instead of S(N
r,:)instead of S(N r
r 1 : N,:) (it basically means replicating the r last rows of the image as in Figure 5).
1 : N,:) (it basically means replicating the r last rows of the image as in Figure 5).
Having obtained S 1 as the unique solution of (17), w 1 (the logo) is extracted as in the nonblind case, and subsequently reshaped to regain the original watermark w. For top and optimum quasiblind embedding the original image is first extracted in a similar manner, and then the w 1 (the logo) is extracted as in the nonblind case.
We note here that since the r parameters of every column have to be known at the receiver/extractor side, as in the bottom embedding case, m parameters of every column have to be known at the receiver/extractor side for both the top embedding and the optimum embedding cases, where m is the number of rows in the logo image. This would mean that an area equal to the logo image (in rows and columns equal to host width) will have to be duplicated in the host image which makes the degradation more noticeable as in Figure 5(b), whereS(1 :m,1 :n) are used instead of  . This justifies why the bottom embedding case is our favorable option for quasiblind extraction. We used the terminology quasiblind as a minor amount of information that has to be known (r parameters of every column) at the receiver side.
. This justifies why the bottom embedding case is our favorable option for quasiblind extraction. We used the terminology quasiblind as a minor amount of information that has to be known (r parameters of every column) at the receiver side.
At this point, it is worth mentioning that there is no guarantee that the r arbitrary variables needed to solve (17), (i.e., r last rows of S
1
) are clustered to the last r right columns o  . They may be randomly distributed all over the columns of
. They may be randomly distributed all over the columns of  . By empirical observation, the simulation results prove that this case happens only when
. By empirical observation, the simulation results prove that this case happens only when  . In this case, the dependent columns have to be identified. The QR matrix decomposition of
. In this case, the dependent columns have to be identified. The QR matrix decomposition of  is used to achieve this goal [27].
is used to achieve this goal [27].
To test the quasiblind scheme, two experiments have been carried out. In the first experiment, we watermark Lena image with a resized university logo. The size of the logo was compressed to  pixels, which makes it possible to reshape it and embed it to the last 6 rows of the host image as explained. NPT is applied to the matrix
pixels, which makes it possible to reshape it and embed it to the last 6 rows of the host image as explained. NPT is applied to the matrix  with
with to get the NPT-transformed image A
w
. The watermarked image A
wm
is constructed by replacing the last 6 rows of A
w
by S(245 : 250,:). Figure 5(a) shows the watermarked Lena image as well as the extracted resized logo. The watermarked PSNR is 34.35 dB.
to get the NPT-transformed image A
w
. The watermarked image A
wm
is constructed by replacing the last 6 rows of A
w
by S(245 : 250,:). Figure 5(a) shows the watermarked Lena image as well as the extracted resized logo. The watermarked PSNR is 34.35 dB.
In the second experiment, we use the complete logo. The logo is reshaped and embedded as the last 21 rows of the host image. Thus,  with
with  . The watermarked image A
wm
is constructed by replacing the last 21 rows of A
w
by S(1 : 21,:). As expected, the rank of V equals the rank of
. The watermarked image A
wm
is constructed by replacing the last 21 rows of A
w
by S(1 : 21,:). As expected, the rank of V equals the rank of  and both equal 214. However, the 21 dependent columns are distributed over the column space of
and both equal 214. However, the 21 dependent columns are distributed over the column space of  . The QR decomposition shows that the columns number I
cm
= [
. The QR decomposition shows that the columns number I
cm
= [ 13 19 26 31 37 42 49 54 60 66 72 79 84 90 96 102 108 114 120 12
13 19 26 31 37 42 49 54 60 66 72 79 84 90 96 102 108 114 120 12 ] are the dependent columns. Hence, we embed the rows of the original image S corresponding to these columns, the PSNR of the reshuffled watermarked image A
wm
is lowered to 25.0 dB. Figure 5(b) shows the watermarked image A
wm
together with the extracted logo. This example clearly indicates that the quality of the watermarked image is high if no data reshuffling occurs. Simulations of several examples have indicated that this would be the case as long as the number of embedded rows does not exceed 6.
] are the dependent columns. Hence, we embed the rows of the original image S corresponding to these columns, the PSNR of the reshuffled watermarked image A
wm
is lowered to 25.0 dB. Figure 5(b) shows the watermarked image A
wm
together with the extracted logo. This example clearly indicates that the quality of the watermarked image is high if no data reshuffling occurs. Simulations of several examples have indicated that this would be the case as long as the number of embedded rows does not exceed 6.
Figure 6 shows the PSNR values of the watermarked image for different values of alpha, along with the corresponding NCORR values of the extracted image, when the watermarked image is compressed using SPIHT with bpp 2.5. It can be shown in the figure that the less the value of alpha, the less contribution of the original image in (2), and the lower the PSNR, but the more contribution of the Hartley basis in (2) which means more energy distribution, which will yield better extraction, better NCORR. A value of alpha in the range 0.985–0.99 is the optimal tradeoff point between the 2 curves, as in Figure 6.
2.5. It can be shown in the figure that the less the value of alpha, the less contribution of the original image in (2), and the lower the PSNR, but the more contribution of the Hartley basis in (2) which means more energy distribution, which will yield better extraction, better NCORR. A value of alpha in the range 0.985–0.99 is the optimal tradeoff point between the 2 curves, as in Figure 6.
4. Testing the Robustness of the Proposed Watermarking Technique
The proposed NPT watermarking extraction algorithm has been tested against cropping compression and noise attacks. The following simulation results show its robustness to these attacks.
4.1. Robustness to Cropping
The main feature of the proposed NPT watermarking scheme is the even distribution of the watermark all over the host image. So, as long as the size of the cropped watermarked image is greater than the size of the embedded logo, cropping has no effects on the extracted logo and one can extract the logo exactly, as the number of linear equations needed to determine the logo is greater than or equal to the number of unknowns. To verify this feature, two examples have been considered. In the first, we consider half cropping the watermarked optimum location embedded Lena image A
wm
. The cropped part is filled with white pixels. Figure 7(a) shows the watermarked cropped image together with the extracted logo.  , a property that is shared by the other two embedding techniques. The second example considers the top embedding of a text on the Cameraman
, a property that is shared by the other two embedding techniques. The second example considers the top embedding of a text on the Cameraman  image. Embedding is achieved using the Matlab string and character functions. The embedded text size is
image. Embedding is achieved using the Matlab string and character functions. The embedded text size is  . Figure 7(b) shows the watermarked and the received cropped watermarked images, as well as the extracted text that has been exactly reconstructed. This perfect reconstruction is valid as long as the size of the cropped image is greater or at least equal to the logo size to ensure a solution of the linear system of equation that determines the logo. This result is to be compared to about
. Figure 7(b) shows the watermarked and the received cropped watermarked images, as well as the extracted text that has been exactly reconstructed. This perfect reconstruction is valid as long as the size of the cropped image is greater or at least equal to the logo size to ensure a solution of the linear system of equation that determines the logo. This result is to be compared to about  for the composite technique of [15], at most
for the composite technique of [15], at most  can be achieved using the curvelet method [16] and with almost
can be achieved using the curvelet method [16] and with almost  in the VQ technique of [14].
in the VQ technique of [14].
4.2. Robustness to Compression Attacks
To verify that the watermarking logo can be easily identified even in presence of compression, the watermarked image A
wm
is compressed using SPIHT coder/decoder [28] algorithm implemented with different number of bits per pixel (bpp). Figure 8 compares the nonblind performance of NCORR of the extracted logos versus compression; (bpp) is used to represent the watermarked Lena image A
wm
, for the three embedding techniques, evaluated for different values of  . These results indicate that embedding the logos near the corners of the host image improves its robustness to compression attacks, since the Hartley matrix concentrates the energy near the 4 corners of the host image (as described before). The results also indicate that the top embedding case competes well with other techniques, especially when decreasing
. These results indicate that embedding the logos near the corners of the host image improves its robustness to compression attacks, since the Hartley matrix concentrates the energy near the 4 corners of the host image (as described before). The results also indicate that the top embedding case competes well with other techniques, especially when decreasing  (a in the figure).
(a in the figure).
4.3. Robustness to Noise Attacks
In this simulation, the watermarked image A
wm
is contaminated with zero mean AWGN as well as salt and pepper noise. The simulation is performed for 10 independent noises, with different seeds, and the extracted logos are averaged over these 10 simulations. Figure 9 compares the normalized correlation of both top and bottom embedding, when the watermarked image is mixed with AWGN with different powers. Figure 10 shows the watermarked images as well as the extracted logos when corrupted for the cases of AWGN yielding  dB and salt and pepper noise with noise density
dB and salt and pepper noise with noise density  ; note that
; note that  is a in the figure. These results compete with composite approach of [15] and are far superior to the curvelet technique in [16], which can achieve at most NCORR
is a in the figure. These results compete with composite approach of [15] and are far superior to the curvelet technique in [16], which can achieve at most NCORR  0.52 for the AWGN attack.
0.52 for the AWGN attack.
4.4. Online Implementation
Due to the simplicity of the proposed NPT technique, it has been implemented on a Digital Signal Processor board (DSP), TMS320C6416T DSP starter kit (DSK). This board has 512 KB flash memory, 16 MB SDRAM, and C6000 Floating point digital signal processor 225 MHZ. Figure 11 shows example of the watermarked image (unmasked and masked with the logo), along with the extracted logo. We note here that because of memory restrictions on the DSK board, the size of the logo on the board was limited. We also note that due to the finite representation of floating point numbers on the DSK, our technique suffers from some truncation noise. Table 1 provides different sizes of the host and watermark images along with their corresponding embedding time and extraction time.
4.5. Blind Noisy Experiment
Figures 12 and 13 show more of our proposed blind watermarking technique. The quality of the extracted logo in noisy environment would be high if no data shuffling happens as described in Section 3.2.2. we can easily see the tradeoff between making the watermark logo more robust in noisy environment (less  value) and making the watermarked image more identical to the original (high
value) and making the watermarked image more identical to the original (high  value).
value).
5. Discussion
We tested our approaches against cropping, noise and compression attacks as evident in Section 4. These attacks resistant results apply for both nonblind logo extraction and quasiblind logo extraction cases, as in the quasiblind case the only difference is just some host image columns duplication as in Section 3.2.2. We note here that the proposed approaches deliver an extracted watermark that is not only perfect/semi perfect but also can be visually seen by the user, which gives the application more user confidence and trustworth. This could be exploited in some applications where the user needs to examine visually the watermark for extra cushion and security, like in law enforcement security applications. The proposed technique can also be used for different data hiding applications where the watermark logo image can be any type of data or side information. It is beyond the scope of this paper to examine effect of rotation, translation, or scaling of the watermarked image on the proposed technique.
6. Concluding Remarks
The paper presents how logos and watermarks can be efficiently embedded using an NPT-based technique. The watermark is highly invisible and robust against cropping, compression, and noise attacks. An efficient fast least square algorithm is also described for watermark extraction, for both the nonblind and quasiblind cases. In the nonblind case, the extraction algorithm assumes prior knowledge of the host image whereas in the quasiblind case only very few information of the host image is needed. Simulation and practical implementation results have proven the robustness of this technique to attacks, especially when the logo is embedded near the corners of the host image. The authors would like to acknowledge the helpful and constructive comments from reviewers. This work is funded in part by the ministry of Communication and Information Technology, Egypt, ITIDA
References
Nikolaidis N, Pitas I: Robust image watermarking in the spatial domain. Signal Processing 1998, 66(3):385-403. 10.1016/S0165-1684(98)00017-6
Hwang M-S, Chang C-C, Hwang K-F: A watermarking technique based on one-way hash functions. IEEE Transactions on Consumer Electronics 1999, 2(45):286-294.
Hernandez JR, Amado M, Perez-Gonzalez F: DCT-domain watermarking techniques for still images: detector performance analysis and a new structure. IEEE Transactions on Image Processing 2000, 9(1):55-68. 10.1109/83.817598
Hsieh M-S, Tseng D-C, Huang Y-H: Hiding digital watermarks using multiresolution wavelet transform. IEEE Transactions on Industrial Electronics 2001, 48(5):875-882. 10.1109/41.954550
Ahmed AM: Digital image Watermarking using fuzzy logic and naturalness preserving transform, Ph.D. thesis. Kansas State University, Manhattan, Kan, USA; 2004.
Cox IJ, Kilian J, Leighton FT, Shamoon T: Secure spread spectrum watermarking for multimedia. IEEE Transactions on Image Processing 1997, 6(12):1673-1687. 10.1109/83.650120
Joo S, Suh Y, Shin J, Kikuchi H: A new robust watermark embedding into wavelet DC components. ETRI Journal 2002, 24(5):401-404. 10.4218/etrij.02.0202.0502
Hsu C-T, Wu J-L: Multiresolution watermarking for digital image. IEEE Transactions on Circuits and Systems II 1998, 45(8):1097-1101. 10.1109/82.718818
Lu C-S, Huang S-K, Sze C-J, Liao H-YM: Cocktail watermarking for digital image protection. IEEE Transactions on Multimedia 2000, 2(4):209-224. 10.1109/6046.890056
Zeng W, Liu B: A statistical watermark detection technique without using original images for resolving rightful ownerships of digital images. IEEE Transactions on Image Processing 1999, 8(11):1534-1548. 10.1109/83.799882
Stanković S, Djurović I, Pitas L: Watermarking in the space/spatial-frequency domain using two-dimensional Radon-Wigner distribution. IEEE Transactions on Image Processing 2001, 10(4):650-658. 10.1109/83.913599
Wang Y, Pearmain A: Blind image data hiding based on self reference. Pattern Recognition Letters 2004, 25(15):1681-1689. 10.1016/j.patrec.2004.06.012
Wong PHW, Au OC, Yeung YM: A novel blind multiple watermarking technique for images. IEEE Transactions on Circuits and Systems for Video Technology 2003, 13(8):813-830. 10.1109/TCSVT.2003.815948
Wu YH-C, Chang C-C: A novel digital image watermarkingscheme based on the vector quantization technique. Computers & Security 2005, 24: 460-471. 10.1016/j.cose.2005.05.001
First E, Qi X: A composite approach for blind grayscale logo watermarking. Proceedings of the IEEE International Conference on Image Processing (ICIP '07), 2007 265-268.
Hien TD, Kei I, Harak H, Chen Y-W, Nagata Y, Nakao Z: Curvelet-domain image watermarking based on edge-embedding. Proceedings of the 11th International Conference on Knowledge-Based Intelligent Information and Engineering Systems (KES '07), 2007 311-317.
Paquet A, Ward R: Wavelet-based digital watermarking for image authentication. Proceedings of the IEEE Canadian Conference on Electrical and Computer Engineering, May 2002 2: 879-884.
Fridrich J: A hybrid watermark for tamper detection in digital images. Proceedings of the International Symposium on Signal Processing and Applications, August 1999 301-304.
Lin C-Y, Chang S-F: Semi-fragile watermarking for authenticating JPEG visual content. Security and Watermarking of Multimedia Contents II, January 2000, Proceedings of SPIE 3971: 140-151.
Lin C-Y, Chang S-F: A robust image authentication method distinguishing JPEG compression from malicious manipulation. IEEE Transactions on Circuits and Systems for Video Technology 2001, 11(2):153-168. 10.1109/76.905982
Koch E, Zhao J: Towards robust and hidden image copyright labeling. Proceedings of the IEEE Workshop on Nonlinear Signal and Image Processing, June 1995 452-455.
Sun QB, Chang SF: Semi-fragile image authentication using generic wavelet domain features and ECC. Proceedings of the IEEE International Conference on Image Processing, September 2002 2: 901-904.
Yarlagda R, Hersshey J: Natural preserving transform for image coding and reconstruction. IEEE Transactions on Acoustics, Speech, & Signal Processing 1985, 4(33):1005-1012.
Day DD, Ahmed AM: A modified natural preserving transform for data hiding and image watermarking. Proceedings of the 4th Joint Conference on Information Sciences of IASTED International Conference Signal and Image Processing, 2003 44-48.
Fahmy M, Raheem G, Mohammed O, Fahmy O, Fahmy G: Watermarking via bspline expansion and natural preserving transform. Proceedings of the IEEE International Symposium on Signal Processing and Information Technology, December 2008, Sarajevo, Bosnia
Fahmy MF, Fahmy OM, Fahmy G: A quasi blind watermark extraction of watermarked natural preserve transform images. IEEE International Conference on Image Processing (ICIP '09), November 2009
Daniels JW: Applied Linear Algebra. Prentice-Hall, Engle wood Cliff, NJ, USA; 1988.
Said A, Pearlman WA: A new, fast, and efficient image codec based on set partitioning in hierarchical trees. IEEE Transactions on Circuits and Systems for Video Technology 1996, 6(3):243-250. 10.1109/76.499834
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
Open Access This article is distributed under the terms of the Creative Commons Attribution 2.0 International License (https://creativecommons.org/licenses/by/2.0), which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.
About this article
Cite this article
Fahmy, G., Fahmy, M. & Mohammed, U. Nonblind and Quasiblind Natural Preserve Transform Watermarking. EURASIP J. Adv. Signal Process. 2010, 452548 (2010). https://doi.org/10.1155/2010/452548
Received:
Revised:
Accepted:
Published:
DOI: https://doi.org/10.1155/2010/452548


 as
as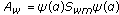 .
.
 .
.


 submatrices
submatrices 

 are in error (nonwatermarked) while Y
21
and Y
22
are in error (nonwatermarked) while Y
21
and Y
22
 convey the watermark effects.
convey the watermark effects.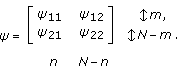

 and from (6), (7), and (9), we can easily show that
and from (6), (7), and (9), we can easily show that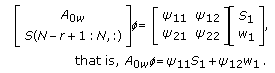
 square matrix V such that
square matrix V such that  . This matrix can be easily constructed by expressing its k th vector V
k
as follows:
. This matrix can be easily constructed by expressing its k th vector V
k
as follows: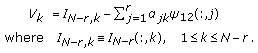
 are obtained by solving a set of r linear equations satisfying the following condition:
are obtained by solving a set of r linear equations satisfying the following condition:
 is an
is an  byr matrix, then its rank
byr matrix, then its rank  . Consequently, the rank of the matrixV is (N
. Consequently, the rank of the matrixV is (N 2r)[
2r)[ to yield
to yield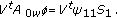
 is (
is ( ), the rank of
), the rank of  is (
is ( ). So, to have a unique solution of (17), r arbitrary parameters of every column of S
1
have to be known at the receiver/extractor. This can be achieved if in the watermarked image A
w
, we choose the matrix z (6) to beS(N
). So, to have a unique solution of (17), r arbitrary parameters of every column of S
1
have to be known at the receiver/extractor. This can be achieved if in the watermarked image A
w
, we choose the matrix z (6) to beS(N 2r
2r 1 : N
1 : N r,:)instead of S(N
r,:)instead of S(N r
r 1 : N,:) (it basically means replicating the r last rows of the image as in Figure
1 : N,:) (it basically means replicating the r last rows of the image as in Figure 







